HPN-SSH
High Performance Networking extensions for OpenSSH — accelerating secure shell for high-latency and high-bandwidth networks
HPN-SSH is a research project based at the Pittsburgh Supercomputing Center
Open Source & OpenSSH-Based
HPN-SSH is an optimized implementation of SSHv2 built directly on top of the industry-standard OpenSSH codebase. HPN-SSH works just like OpenSSH and is released under the BSD 2 clause license allowing anyone to use it without restriction.
Designed for Performance
HPN-SSH removes traditional throughput limitations and improves performance on long-distance, high-latency, and high-bandwidth networks. It also makes use of parallelized cryptographic function improving perfomance over the local area network as well.
Drop-In Compatibility
HPN-SSH works just like OpenSSH and is cross compatible with any SSHv2 compliant implementation. It can also provides performance benefits when used with other versions of ssh like OpenSSH or WinSCP.
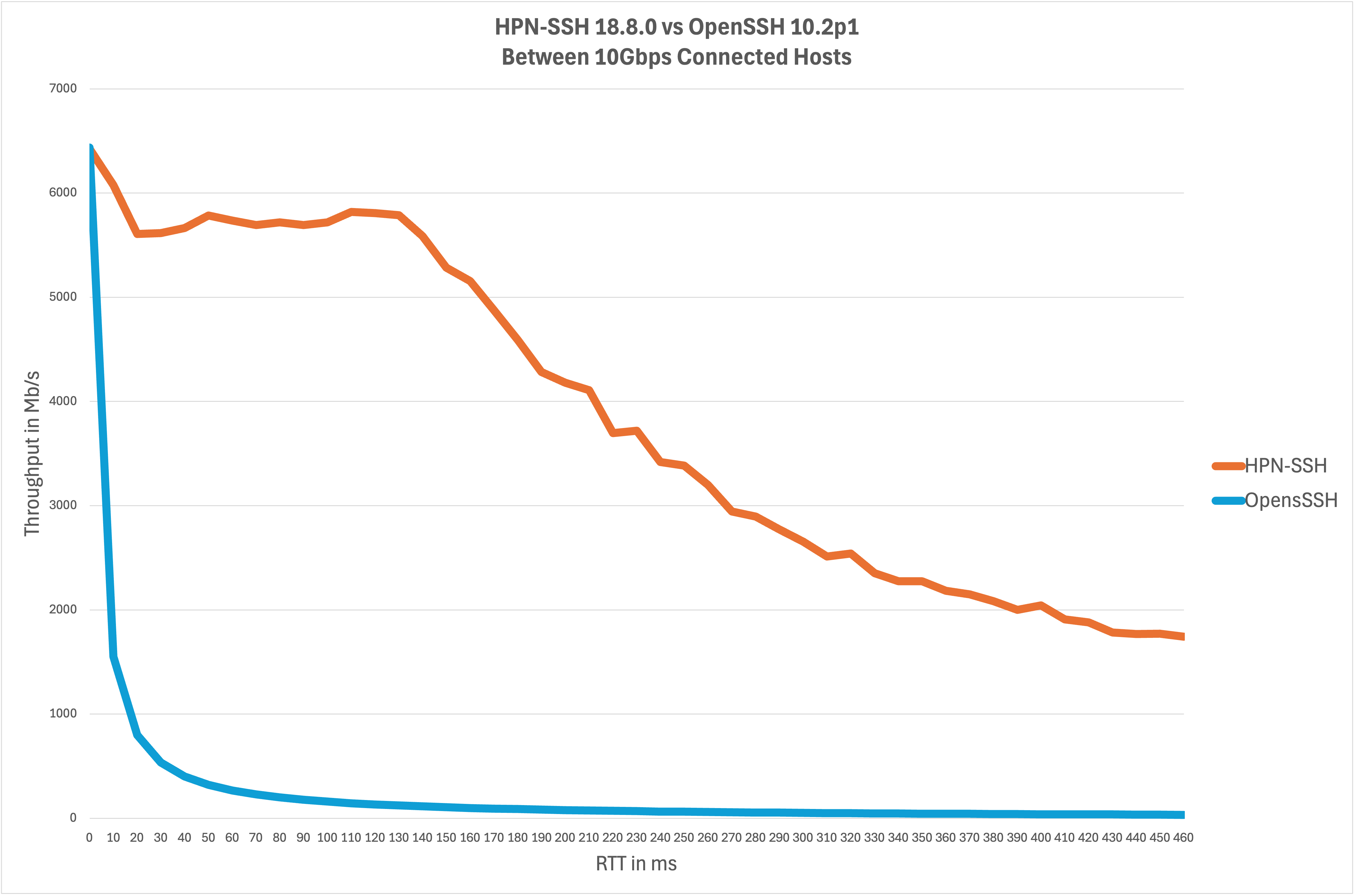
HPN-SSH Outperforms OpenSSH
Key Features
High performance ciphers
Parallel ciphers and encryption options dramatically improve performance.
Dynamic Window Scaling
Automatically adjusts SSH window sizes to fully utilize available bandwidth.
High Throughput Transfers
Dramatically improves bulk data transfers with SCP, SFTP, rsync and other data transfer tools.
Common Use Cases
High Speed Data Transfers for Research and Industry
Fast, secure access to compute clusters and research infrastructure.
Scientific & Research Networks
Ideal for data-intensive workflows across national and international links.
Enterprise & Cloud Operations
Efficient file transfers across distributed systems.
Quick Start
Git:
git clone https://github.com/rapier1/hpn-ssh
cd hpn-ssh
./configure && make && sudo make install
Ubuntu:
sudo add-apt-repository ppa:rapier1/hpnssh
Fedora:
sudo dnf copr enable rapier1/hpnssh
Debian:
See our installation instructions.
This work was made possible in part by grants from Cisco Systems, Inc., the National Science Foundation, and the National Library of Medicine.